A managed risk approach all across the network will take your business and Mindset to the next level
Today, everyone is afraid, and it seems that the Zero Trust Mindset characterizes all levels of our society, from personal to corporate relationships, from the private to the public sphere.
I don’t know about you, but I’m far from my best version when I’m scared and unsure. hashtagZeroTrustMindset
I need to control my potential if I want my business and personal relationships to be as successful as they’re now. hashtagTrustmyPath
You could say that the cybersecurity business is triumphant everywhere, but those are just the successful numbers. “We won’t get compromised”, everyone says.
What about the millions of startups and large companies that have closed their doors because they were too scared to believe they could win in the digital war?
And it is a Digital War…whether you are aware of it or not. And it’s you against North Korea, Iran, Russia, China, and the officially organized crime gangs.
The Same Mindsets Win Year over Year, Decade over Decade, for Ages.
No matter what world catastrophe is hovering over you, it still holds: you can and will overcome anything life throws at you.
It’s still true that only your mindset determines the outcome.
In any situation, you still have the necessary resources to overcome difficulties.
When times get tough, as they’ve been for all of us, we need to move to a higher level and think strategically.
Don’t panic; solve problems. Move, Action, Direction, Remediate.
The dystopian paradigm has already conquered you if you do not shake up and change your way of thinking.
I always remember the story my mentor told me when I was just starting out and learning the trade tricks.
He was a CISO at a company when building a basic security stack was enough. Whenever there was a major security issue that caused everyone to panic, he would gather his entire team and tell that story.
A CIO Comes to a Therapist
CIO: It doesn’t go away; nothing helps.
THERAPIST: Are you sure you don’t want to give up and find another line of work?
CIO: No. I love my job. There’s just too much bad news and too much negativity around me.
THERAPIST: The stress is overwhelming?
CIO: I can’t take the pressure anymore.
THERAPIST: Everybody complains about it. It’s the number one problem today.
CIO: I feel so mediocre.
THERAPIST: You feel what you know.
CIO: Are you implying that I am mediocre?
THERAPIST: I’m explicitly verifying it.
CIO: I resent that. I am a CIO with 3,000 desktops.
THERAPIST: I would feel very strongly if I were you.
CIO: What about the responsibility? Financial and human?
THERAPIST: All parents handle it well.
CIO: You are not helping me reduce my stress.
THERAPIST: And because you think it’s my fault, you’ll always be mediocre.
CIO: I’m getting angry.
THERAPIST: Are you angry enough to solve your problems?
CIO: How am I supposed to do that?
THERAPIST: I will give you a book about each emotional problem you suffer from, and when you have read them all, you will know how to rise from mediocrity.
…
Knowledge is protection. Learn. Security starts with the basics. Learn for life.
You Don’t Have To Settle for Fear
Do you know what the opposite of fear is? — Freedom.
And this is where technology comes in.
The original reason for technology was freedom.
Technology was not meant to enslave you. Do not buy just any theory.
Instead, use your common sense as a guide.
If the product does not free you from unnecessary actions, you have the wrong product, wasting your resources and staying on the hamster wheel.
Move on. Upgrade. Form better partnerships. Level Up.
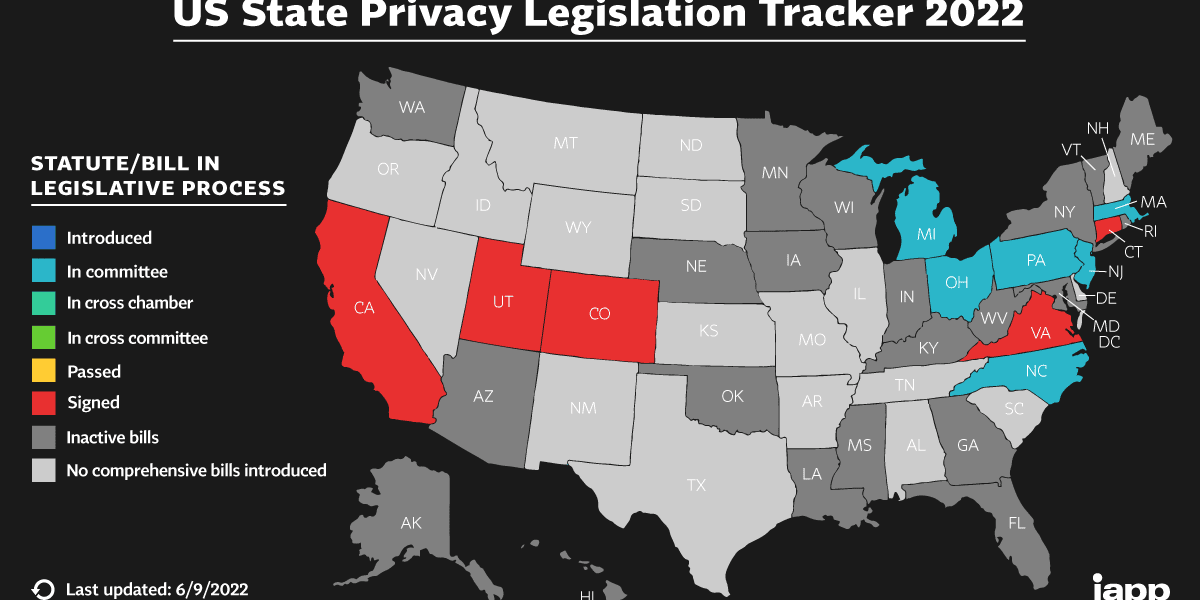
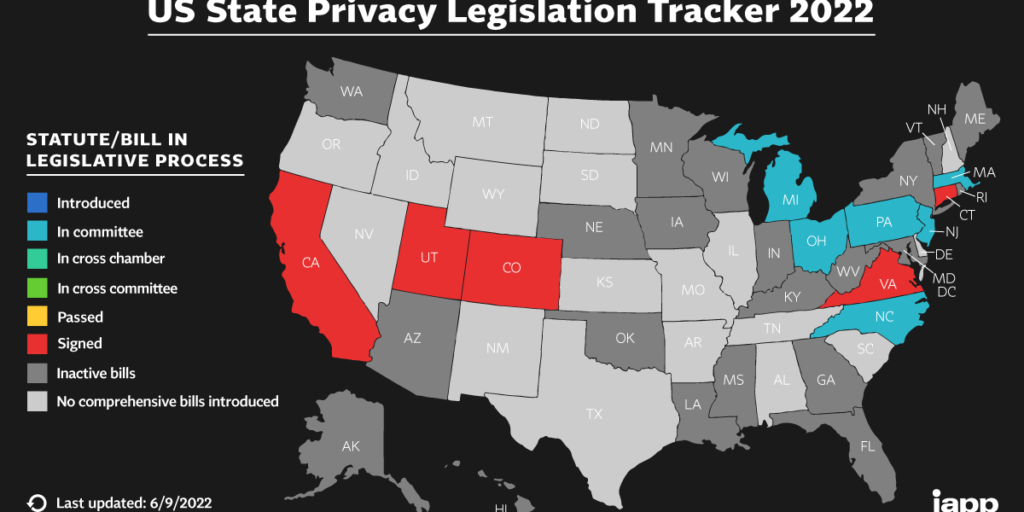
Zero Trust Architecture is the next trustworthy step you should take regardless of the size and number of your attack surfaces.
And here are the top reasons, although I could think of many more.
- The Zero Trust mindset and architecture are revolutionary in cybersecurity.
- Zero Trust has climbed the ladder in thinking security.
- To have trust, you need zero trust.
- Zero Trust is designed to defend against any threat, including human error and accidental data loss.
- Zero Trust means you have to assume an attack and verify everything explicitly. Identity has become the battleground of security.
Your average firewall is not enough.
Your average email suit is not enough.
You need to implement a Zero Trust framework to have trust in protecting your network and your business.
Have zero trust in the activity that takes place and arrives on your network.
Always assume a security breach and recognize that attacks are inevitable.
For this reason, Zero Trust explicitly verifies every activity.
You will be checked every time you try to enter the network if you are an employee. Every time.
And you will not have access to everything, only conditionally and contextually.
Only what you need to do your job will be available.
Configuration Makes the Difference
Zero Trust is about suits and functions.
Everything is always a question of configuration.
And just like in life, everything is negotiable and flexible. The quality of your configuration determines the quality of your protection.
Don’t blame the software and the different vendors; get competent partners to make your security stack run smoothly.
To make your security stack compliant, you need to invest in the following:
- Software licensing and renewals
- Implementation and configuration (updates and reconfiguration)
- Monitoring and project management
You must do something if you do not want your world to become dystopian.
And if you take all the right steps and follow the best security practices under expert guidance, you will go the last mile and rise without a doubt.
Our expertise is software subscription licensing, renewals, and managed security services.
Our goal is to use this expertise to guide you on the final journey to compliance with NIST and CSF (cybersecurity framework).
When choosing new security software, it’s always best to be guided by regulatory standards.
At TLIC Worldwide, Inc., we follow the NIST 800–207 standard for Zero-Trust.
You should ask yourself what products you have and what products you need to meet the requirements of NIST and CSF.
Once you reach the compliant level, you will not be afraid.
Because you will know what you did to get to the next level, and you will know how to repeat it.
Knowledge is protection.
If the reward is bigger than the risk, always take the risk.
Security is about education, long-term relationships, and a successful last mile for life.
As Jay McBain put it, “In this decade of the ecosystem, no one can do it alone.”
Thanks for Reading!
Hold on a second! You should get my articles sent straight to your newsfeed. Subscribe here to stay updated and ahead in technology with your business.